CONS3RT sites supporting government users (e.g Arcus) requires the use of PKI certificate credentials for authentication. These can include:
- DoD Common Access Card (CAC)
- External Certificate Authority (ECA) (https://public.cyber.mil/eca/)
- DoD External and Federal PKI Interoperability approved organization (https://public.cyber.mil/pki-pke/)
- MITRE corporate credentials
The 6 sections below cover most common user questions regarding certificates.
- How to Register with a Certificate
- Obtaining an ECA Certificate
- Obtaining a DOD Certificate
- Logging in to Arcus with a Certificate
- Adding a New Certificate or CAC to your account
- Managing your Account Certificates
- Troubleshooting Certificate issues
If you can’t answer your question by perusing this KB, please feel free to submit a support ticket to support@arcus-cloud.io.
1. How to Register with a Certificate
Register your CAC or ECA Certificate
- Ensure your CAC or ECA cert is loaded into your browser
- Navigate to the Arcus site
- Select the certificate that you would like to register, and enter the CAC PIN or ECA passphrase as needed
- Click OK after the Notice and Consent Page
- Click the Register button in the top-right, and follow the instructions
- You should receive an email with additional instructions for working in Arcus
2. Obtaining an ECA Certificate
Arcus requires use of a PKI credential. Users without a Common Access Card (CAC) can can authenticate using External Certificate Authority (ECA) certificates. Using ECA Certificates has many benefits:
- Convenient site access using your browser or mobile device
- Convenient method for making ReST API calls
Info on Obtaining an ECA certificate
- Arcus is a partner of IdenTrust; click here for info on obtaining an IdenTrust ECA certificate for Arcus
- DISA ECA certificate information
The software-based Medium Assurance ECA Certificates are the best solution for most contractors, developers and testers. An ECA Medium Assurance Software Certificate or the ECA Medium Token Assurance stored on a separate Smart Card or USB Token can also be used. For machine-to-machine API connections, ECA Medium Assurance TLS/SSL is required.
DoD External and Federal PKI Interoperability
If your agency or employer is part of the DoD External and Federal PKI Interoperability program, those credentials can also be used in Arcus:
Add an ECA Certificate to your CONS3RT Account
Follow the steps in #4 below to add the ECA cert to your account
3. Obtaining a DOD Certificate
Go to: https://npe-portal.csd.disa.smil.mil/NPEPortal/#!/certenroll
Steps
- From Certificate Management Pulldown → Conduct Certificate operations → select “Submit Certificate Application…”
- Copy/paste in CSR form the text doc you brought over from the low side (when the key was generated - safeguard the key). Pasting in should populate some fields including Certificate Profile (basically the SAN Names)
- From Certificate Profile pulldown → select either “TLS/Server or “Device” based on the server role (this will populate Certificate Validity fields)
Note: Some browsers will fail if Device/3 year is selected for forward-facing services that people hit with browsers.
- From Certificate CC/S/A* pulldown → select “USSF” or appropriate issuer
- This should populate key usage. Take the default unless you specifically know not to Digitally sign
- Under Extended Key Usage select:
Id-kp-clientAuth Id-kp-serverAuth- (Don’t worry about add-ons unless you know they are specifically needed)
- As soon as you hit submit, it should return a request number. You can retrieve any past request numbers/status of orders by going to Certificate Management → Conduct Certificate Operations → View My Certificate Applications
- Copy+paste the request number into the pdf (Form 2842-2) and digitally sign the form
- To submit:
- Submit here for NIPR: https://afpki.servicenowservices.com/
- Email for SIPR submission: USAF.JBSA.AFLCMC.MBX.AFPKI-Registration@mail.smil.mil
IMPORTANT! Digitally sign the email but do not encrypt it.
Email Subject: DOD CERT REQUIRED
Example body: Request corresponding to NPE Portal submission attached - please let me know if there are any issues and thanks\ - When the certificate is approved, you will receive an email back from USAF JB letting you know the public key has been generated to match the private and you can retrieve it from the portal
- Certificate Management Pulldown → Conduct Certificate Operations → View Certificate Application Status…
- From here you can download the formats needed (usually X509 and binary)
Note: If you need the root certs, they can be found under Certificate Management → View Certificate Authority Details…
4. Logging into Arcus with a Certificate
Arcus uses certificate-based authentication only. There is no username/password access to Arcus.
Logging in to Arcus
- First and foremost, ensure your certificate is loaded into your browser
- If using a CAC, ensure you have the proper middleware installed, and your CAC is inserted into your CAC reader
- If using an ECA certificate, ensure the certificate has been imported into your browser
- Navigate to Arcus
- You will be prompted to select a certificate. Select the same certificate you used to register for an account
- Click Agree on the Notice and Consent page
- Click the Sign In button at the top right
Note: If you selected a different certificate than was registered, your login will fail, but you can add the certificate to your Arcus account using the steps in Section 4 below.
5. Add a New Certificate or CAC to your account
Adding a new Certificate
Use the following steps to add a CAC or ECA certificate to your existing account.
- Navigate to Arcus
- Click the Sign-In button
- When prompted, select the new CAC or ECA certificate that you would like to associate.
- You should see an authentication error, but under that error there is an Account Assistance link.
- Click the Account Assistance link
- Select I Have a New Certificate
- Enter the email to add your CAC or ECA certificate to your existing account (Be sure to use the email address associated with your existing Arcus account)
- Check your email for the link to associate your cert with your account (If no email appears, be sure to check your spam filter. If it’s been more than 15 minutes, contact support)
- Following the link, when prompted, select the new CAC or ECA certificate that you would like to associate
- You will be sent to a page with Client Certificate Details, please confirm that everything is correct, and then click Add Certificate
Once completed, return to Arcus and sign in with your new certificate.
Still having trouble?
First, try closing and re-opening your browser to clear any prior certificate selections.
If that does not work, your existing account might be inactive if you have had more than 30 days of inactivity.
- Follow these instructions to reactivate your account
- Once your account is reactivated, follow the steps above to add your new certificate
If you are still having issues please try verifying that you have the proper root certificates installed. The steps are in this article: Certificate Login Errors
Note: Account reactivation requests may require re-approval from a Government sponsor.
6. Manage Your Account Certificates
Once signed in to your Arcus account, all users can manage their own certificates
- Click on the person icon located at the top right corner of the page
- Choose Profile & Account from the list
- On the left panel of the profile page, select Security
- On the security page, scroll down to the PKI certificates section.
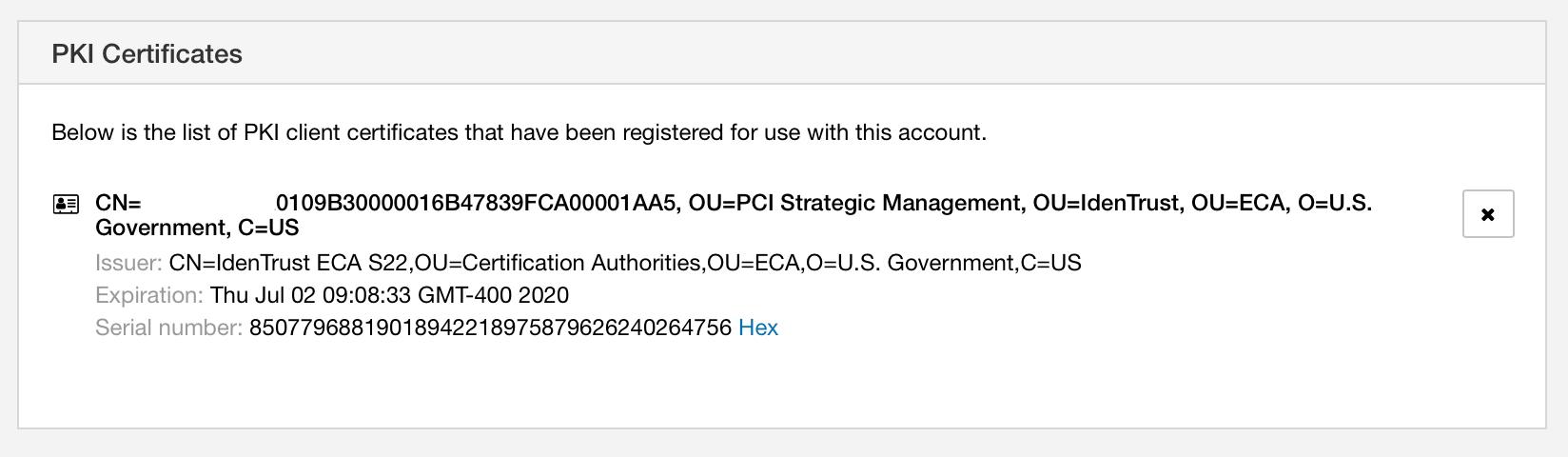
You can now review which certificates are registered to your account (e.g. your CAC email or ID certificate). If there are any you wish to remove from the account click the “X” located at the right side of the certificate.
7. Troubleshooting Certificate issues
For sites that support or require PKI authentication, users sometimes encounter errors with related to presenting certificates. The DoD Cyber Exchange site has good information on getting started with PKI/PKE.
Can’t Log In With Your CAC?/Client Certificate Not Found?
CONS3RT sites supporting government users (e.g Arcus) requires the use of PKI certificate credentials for authentication. There is no username/password access to Arcus. Credentials can include:
- DoD Common Access Card (CAC)
- External Certificate Authority (ECA) (https://public.cyber.mil/eca/)
- DoD External and Federal PKI Interoperability approved organization (https://public.cyber.mil/pki-pke/)
- MITRE corporate credentials
What Causes the “Client Certificate Not Found” Error?
The “Client Certificate Not Found” error will occur when the site is looking for the registered PKI required for access, and failing to find the Certificate. The most likely issue is a misconfiguration of the Operating System or Browser. Please see the sections below for possible solutions:
- Configuring Browsers
- Locked CAC
- Cross Certificate Issue *Try this one if the browser appears to be configured correctly
Before we get started troubleshooting, There are a couple of basic preliminary steps to follow:
- Try clearing the cache on your browser (this can usually be done via the settings or history tab, and is sometimes called clearing browser history). Be sure to remember to close your browser and open it again for the best results
- Try a different browser! It’s quite common to install your Certs via Chrome or Safari, and login to a computer with a different default browser and forget that the Certs were installed somewhere else!
- Try incognito mode. If you’re using Chrome, Incognito mode is a useful troubleshooting mode because it eliminates any possible issues with cookies or sessions being cached.
- Make sure your CAC is inserted! It can and does happen. If you are attempting to connect with a CAC, please make sure that it is inserted and readable by your operating system.
- Make sure that you are typing your CAC password correctly. If you mistype the PIN or password on a soft certificate, the certificate does not get sent over and you will not be able to login.
Configuring Browsers
Additional instructions for configuring your browser to use PKI.
Locked CAC
DoD-issued Common Access Cards (CACs) are designed to lock after three incorrect PIN entries. In some operating system/browser combinations it is not clear that the CAC is locked when being presented in the browser. To check if a CAC is locked, try unlocking the CAC via the local certificate middleware (e.g. ActiveClient on Windows or Keychain.app on MacOS).
Cross Certificate Issue
Occasionally, certificate configurations on Windows systems can become unusable, typically (but not always) when a user is issued new credentials from a different Certificate Authority (CA). This is a known issue that looks like the browser is presenting a certificate to the website, but really is not. This issue can be fixed by running the Cross Certificate Removal Tool.
- Download the Cross Certificate Remover Tool
Note: If you selected a different certificate than was registered, your login will fail, but you can add the certificate to your Arcus account using the instructions in section #4 above.
Note: Some Windows users are able to resolve certificates and/or TLS connection isues by adding the site to the Trusted Sites list in the browser.
Didn’t recieve an email after adding a new certificate?
There are several possibilities that could result in no email being recieved after requesting a new certificate.
- Wrong Email
- The email address attached to your Arcus account is outdated or mispelled (It happens more often than you might think)
- Spam Email
- Check your spam folder. Sometimes emails can end up being caught by the spam filter.
- Blocked Email
- The emailer that automatically sends these emails may be blocked by your network or firewall settings at your workplace
Unless the email is simply caught in the spam filter, the simple resolution is to put in a support ticket by using the “Contact Us” Widget on the Arcus page, or send an email to support@arcus-cloud.io.
Encountering a “CAC not detected” or “TLS Issue” Message in the Browser?
See this Knowledge Base Article for our recommended resolution.
More Help
Review this topic with our video tutorials: